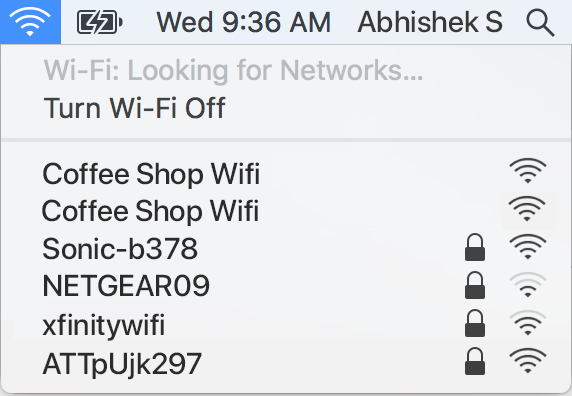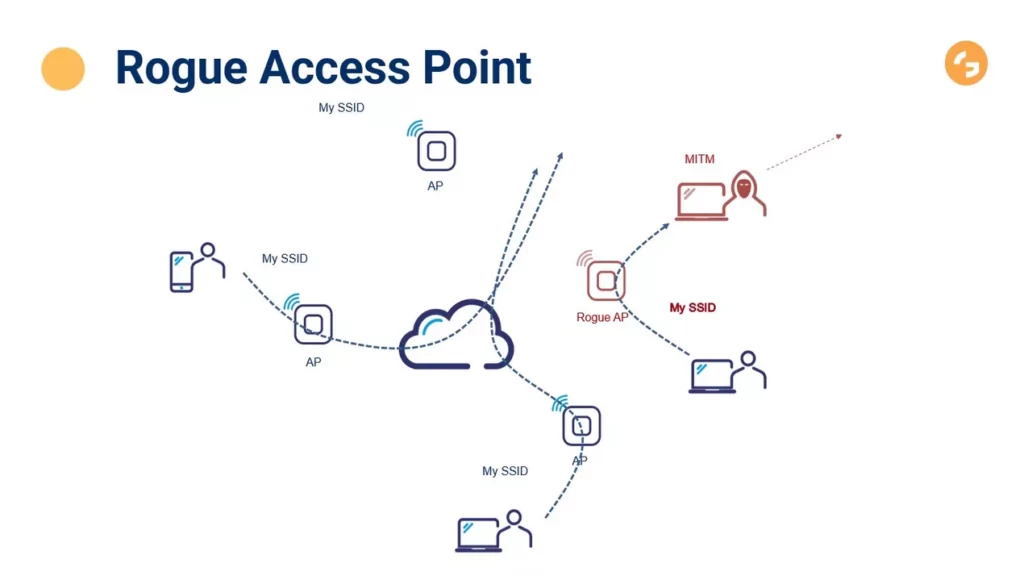
Modern Wireless Tradecraft Pt I — Basic Rogue AP Theory — Evil Twin and Karma Attacks | by Gabriel Ryan | Posts By SpecterOps Team Members

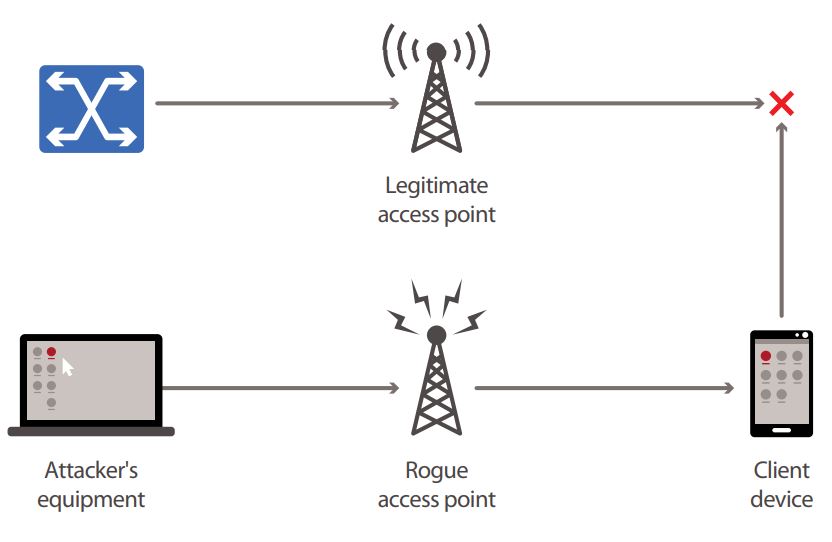
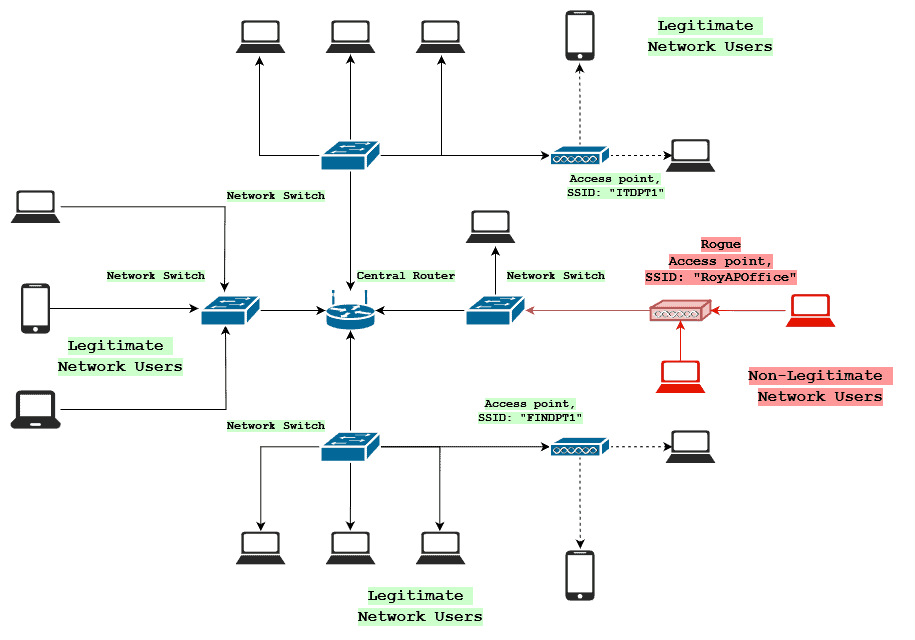
This figure shows the setup of a rogue AP. A rogue AP is connected to... | Download Scientific Diagram

Client-side rogue access-point detection using a simple walking strategy and round-trip time analysis | EURASIP Journal on Wireless Communications and Networking | Full Text

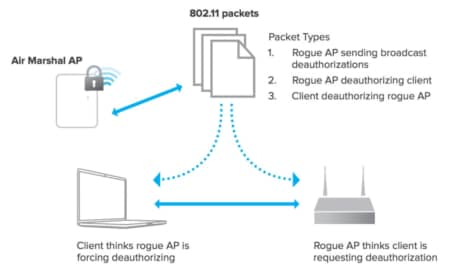
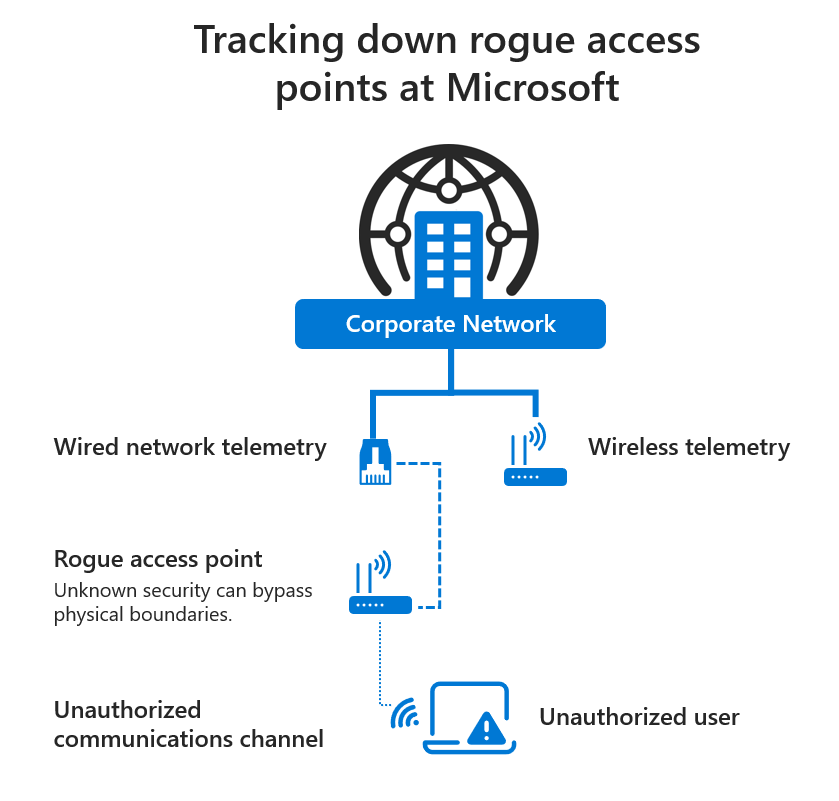
Linksys Official Support - How to enable Rogue AP Detection on your Linksys Wireless-AC Access Point

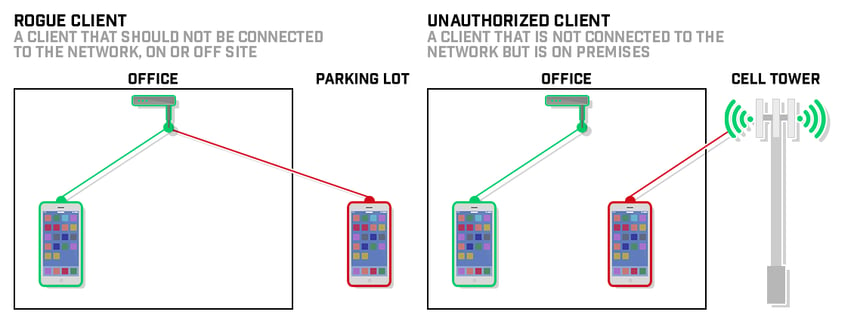
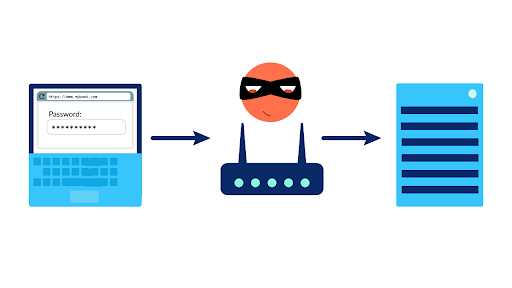
Rogue Access Points and Evil Twins - CompTIA Security+ SY0-501 - 1.2 - Professor Messer IT Certification Training Courses